GWS - Google Platforms Phishing
Tip
Jifunze na ufanye mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na ufanye mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na ufanye mazoezi ya Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Saidia HackTricks
- Angalia the subscription plans!
- Jiunge na 💬 Discord group au the telegram group au utufuate kwenye Twitter 🐦 @hacktricks_live.
- Shiriki hacking tricks kwa kutuma PRs kwa HackTricks and HackTricks Cloud github repos.
Mbinu za Kawaida za Phishing
Phishing Methodology - HackTricks
Google Groups Phishing
Kwa kuonekana, kwa default, kwenye workspace wanachama can create groups and invite people to them. Unaweza kisha kubadilisha email itakayotumwa kwa mtumiaji kwa adding some links. Barua pepe hiyo will come from a google address, hivyo itaonekana legit na watu wanaweza kubofya kwenye kiungo.
Inawezekana pia kuweka anwani ya FROM kama Google group email ili kutuma more emails to the users inside the group, kama kwenye picha ifuatayo ambapo group google--support@googlegroups.com iliumbwa na email was sent to all the members wa group (waliyoongezwa bila idhini yoyote)
 (1).png)
Google Chat Phishing
Unaweza kuwa utaweza kueither start a chat na mtu kwa kuwa tu na anwani yao ya barua pepe au kutuma invitation to talk. Zaidi ya hayo, inawezekana create a Space lenye jina lolote (mfano “Google Support”) na invite wanachama kujiunga. Ikiwa watakubali wanaweza kufikiri wanazungumza na Google Support:
.png)
Tip
Hata hivyo, katika majaribio yangu wanachama waliotumwa hawakupokea hata mwaliko.
Unaweza kuona jinsi hili lilivyofanya kazi hapo awali hapa: https://www.youtube.com/watch?v=KTVHLolz6cE&t=904s
Google Doc Phishing
Kwenye zamani ilikuwa inawezekana kuunda apparently legitimate document na kisha katika maoni mention some email (like @user@gmail.com). Google sent an email to that email address ikiwajulisha kuwa walitajwa katika dokumenti.
Hivi sasa, hili halifanyi kazi lakini ikiwa utampa give the victim email access to the document Google itatuma barua pepe ikibainisha hivyo. Huu ndiyo ujumbe unaoonekana unapotaja mtu:
.png)
Tip
Waathiriwa wanaweza kuwa na mfumo wa ulinzi ambao hauwaruhusu barua pepe zinazoonyesha kuwa dokumenti ya nje ilishirikiwa nao kufika kwenye barua pepe yao.
Google Calendar Phishing
Unaweza create a calendar event na kuongeza anwani za barua pepe nyingi za kampuni unayomlenga kadri ulivyo nazo. Panga tukio la kalenda hili kwa 5 or 15 min kutoka wakati wa sasa. Fanya tukio liwe legit na put a comment and a title indicating that they need to read something (na phishing link).
Huu ndio onyo utakaoonekana kwenye kivinjari na kichwa cha mkutano “Firing People”, hivyo unaweza kuweka kichwa cha habari chenye muonekano wa phishing (na hata kubadilisha jina linalohusishwa na barua pepe yako).
.png)
Ili kuifanya ionekane isiyo ya kutiliwa shaka:
- Panga ili receivers cannot see the other people invited
- Usitume NOT send emails notifying about the event. Kisha, watu wataona tu onyo lao kuhusu mkutano ndani ya dakika 5 na kwamba wanahitaji kusoma kiungo hicho.
- Inaonekana kwa kutumia API unaweza kuweka kuwa True kwamba people wameaccepted the event na hata kuunda comments on their behalf.
App Scripts Redirect Phishing
Inawezekana kuunda script katika https://script.google.com/ na expose it as a web application accessible by everyone itakayotumia domain halali script.google.com.
Kwa kutumia baadhi ya code kama ifuatavyo attacker anaweza kufanya script ipakishe maudhui yoyote kwenye ukurasa huu bila kuacha kutumia domain:
function doGet() {
return HtmlService.createHtmlOutput(
'<meta http-equiv="refresh" content="0;url=https://cloud.hacktricks.wiki/en/pentesting-cloud/workspace-security/gws-google-platforms-phishing/index.html#app-scripts-redirect-phishing">'
).setXFrameOptionsMode(HtmlService.XFrameOptionsMode.ALLOWALL)
}
For example accessing https://script.google.com/macros/s/AKfycbwuLlzo0PUaT63G33MtE6TbGUNmTKXCK12o59RKC7WLkgBTyltaS3gYuH_ZscKQTJDC/exec you will see:
 (1).png)
Tip
Kumbuka kwamba onyo litaonekana wakati maudhui yanapopakiwa ndani ya iframe.
App Scripts OAuth Phishing
It’s possible to create App Scripts attached to documents to try to get access over a victims OAuth token, for more information check:
OAuth Apps Phishing
Any of the previous techniques might be used to make the user access a Google OAuth application that will request the user some access. If the user trusts the source he might trust the application (even if it’s asking for high privileged permissions).
Note
Kumbuka kwamba Google inaonyesha onyo lisilo zuri likitoa tahadhari kwamba application haijathibitishwa katika matukio kadhaa na Workspace admins wanaweza hata kuzuia watu kukubali OAuth applications.
Google inaruhusu kuunda applications zinazoweza kuingiliana kwa niaba ya watumiaji na huduma mbalimbali za Google: Gmail, Drive, GCP…
Wakati wa kuunda application ili itende kwa niaba ya watumiaji wengine, mtengenezaji anahitaji kuunda OAuth app ndani ya GCP na kuainisha scopes (permissions) ambazo app inahitaji kufikia data za watumiaji.
Wakati mtumiaji anataka kutumia application hiyo, ataulizwa kukubali kwamba application itakuwa na ufikiaji wa data zao zilizotajwa katika scopes.
Hii ni njia yenye tija kubwa ya phish watumiaji wasio wa kitaaluma ili waweze kutumia applications zinazopata taarifa nyeti kwa sababu wanaweza kutoelewa madhara. Hata hivyo, katika akaunti za shirika, kuna njia za kuzuia hili kutokea.
Unverified App prompt
Kama ilivyotajwa, Google kila wakati itaonyesha prompt kwa mtumiaji ili akubali ruhusa anazompa application kwa niaba yake. Hata hivyo, ikiwa application itachukuliwa kuwa hatari, Google kwanza itaonyesha prompt inayoonyesha kuwa ni hatari na kufanya iwe ngumu zaidi kwa mtumiaji kutoa ruhusa kwa app.
Prompt hii inaonekana katika apps ambazo:
- Inatumia scope yoyote inayoweza kufikia data binafsi (Gmail, Drive, GCP, BigQuery…)
- Apps zenye watumiaji chini ya 100 (kwa apps > 100, mchakato wa ukaguzi pia unahitajika ili kuacha kuonyesha unverified prompt)
Scopes za Kuvutia
Hapa unaweza kupata orodha ya scopes zote za Google OAuth.
- cloud-platform: Angalia na simamia data yako katika huduma za Google Cloud Platform. Unaweza kuiga mtumiaji katika GCP.
- admin.directory.user.readonly: Tazama na pakua directory ya GSuite ya shirika lako. Pata majina, nambari za simu, na URLs za kalenda za watumiaji wote.
Create an OAuth App
Start creating an OAuth Client ID
- Go to https://console.cloud.google.com/apis/credentials/oauthclient and click on configure the consent screen.
- Then, you will be asked if the user type is internal (only for people in your org) or external. Select the one that suits your needs
- Internal might be interesting you have already compromised a user of the organization and you are creating this App to phish another one.
- Give a name to the app, a support email (note that you can set a googlegroup email to try to anonymize yourself a bit more), a logo, authorized domains and another email for updates.
- Select the OAuth scopes.
- This page is divided in non sensitive permissions, sensitive permissions and restricted permissions. Eveytime you add a new permisison it’s added on its category. Depending on the requested permissions different prompt will appear to the user indicating how sensitive these permissions are.
- Both
admin.directory.user.readonlyandcloud-platformare sensitive permissions.
- Add the test users. As long as the status of the app is testing, only these users are going to be able to access the app so make sure to add the email you are going to be phishing.
Sasa tupate credentials kwa web application tukitumia OAuth Client ID iliyoundwa hapo juu:
- Rudi kwenye https://console.cloud.google.com/apis/credentials/oauthclient, chaguo tofauti litaonekana wakati huo.
- Chagua kuunda credentials for a Web application
- Weka Javascript origins na redirect URIs zinazohitajika
- Unaweza kuweka kwenye zote kitu kama
http://localhost:8000/callbackkwa ajili ya testing
- Pata credentials za application yako
Mwishowe, wesha web application itakayotumia credentials za OAuth application. Unaweza kupata mfano katika https://github.com/carlospolop/gcp_oauth_phishing_example.
git clone ttps://github.com/carlospolop/gcp_oauth_phishing_example
cd gcp_oauth_phishing_example
pip install flask requests google-auth-oauthlib
python3 app.py --client-id "<client_id>" --client-secret "<client_secret>"
Nenda kwenye http://localhost:8000, bonyeza kitufe cha Login with Google, utaonyeshwa ujumbe kama huu:
.png)
Programu itaonyesha access and refresh token ambazo zinaweza kutumika kwa urahisi. Kwa maelezo zaidi kuhusu how to use these tokens check:
Using glcoud
Inawezekana kufanya jambo kwa kutumia gcloud badala ya web console, angalia:
GCP - ClientAuthConfig Privesc
OAuth app protections
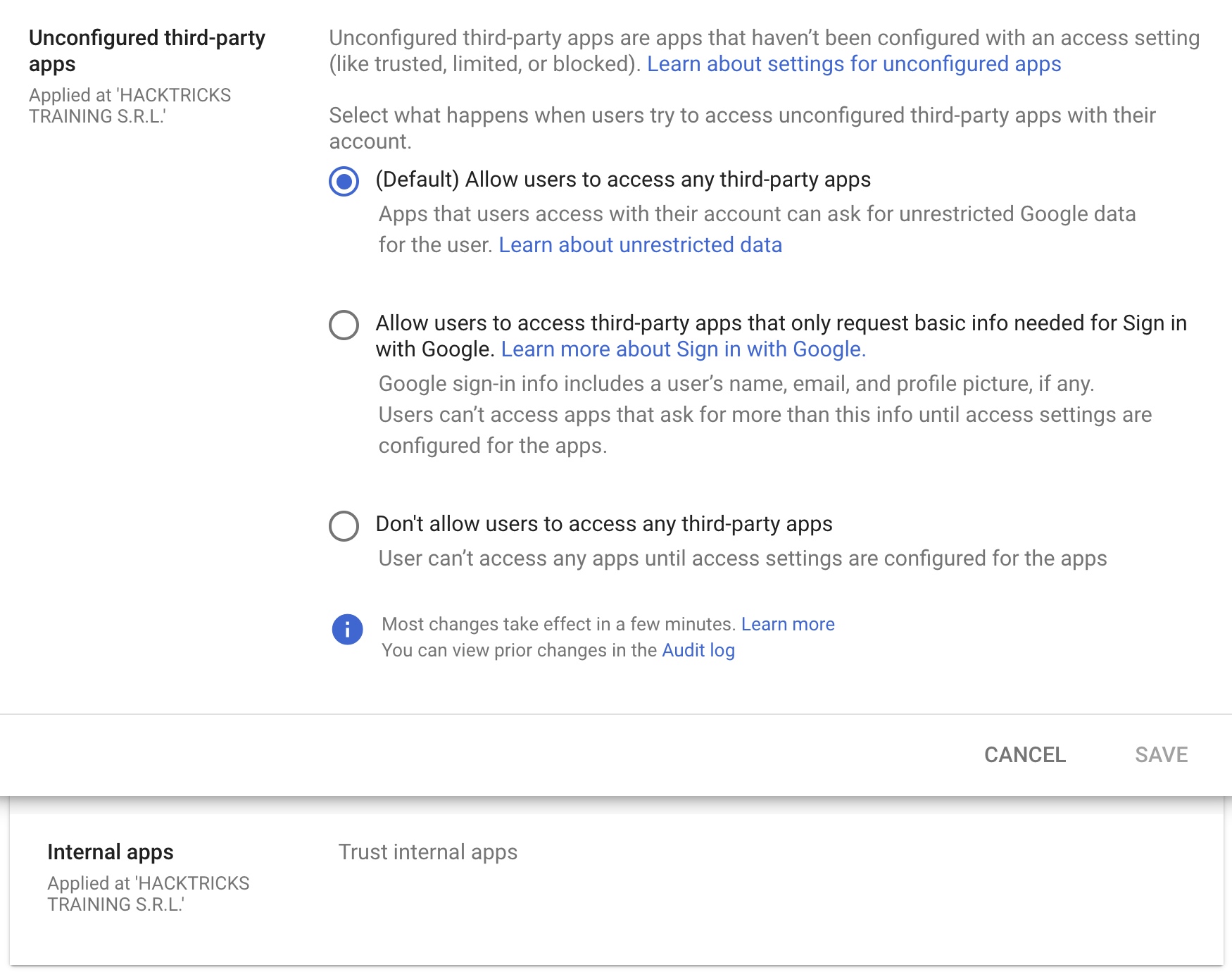
Kawaida imewekwa kwamba mtumiaji yeyote ndani ya shirika la Workspace can accecpt any OAuth app with any permissions, lakini inawezekana kuzifungia kuwa ni apps zinazotaka tu taarifa za msingi zinazohitajika kwa Sign in with Google au kutoruhusu any third-party apps.
Zaidi ya hayo, hata ukizizuia kuamini external third-party apps, inawezekana kuruhusu trust any internal apps (apps created inside the organization). Uaminifu huu umewekwa kwa default.
OAuth Consent Grant Abuse: Detection & Response (Admin Reports)
Wakati mtumiaji anampatia ruhusa OAuth app, Google Workspace inarekodi hiyo katika Admin Reports OAuth Token Audit Activity (application name token) na events.name imewekwa kuwa authorize. Matukio haya ni telemetry bora za kugundua consent phishing na kufuatilia client ID na scopes zilizotolewa.
Key fields to extract from the audit event:
id.time,id.customerIdactor.email,actor.profileIdipAddress,networkInfo.regionCode,networkInfo.subdivisionCodeevents[0]['parameters']values forclient_id,app_name,scope,scope_data
Anza kwa msingi kwanza (punguza kelele): tengeneza orodha ya existing client IDs na scopes, kisha toa arifa kwa consents mpya/zisizo za kawaida.
gam all users print tokens todrive
Mawazo ya utambuzi (app mpya/nadra + scopes zenye hatari):
- Taarifu ikiwa
client_idhaipo kwenye allowlist iliyokubaliwa na haijaonekana kwa siku X zilizopita (kwa mfano, 90). - Taarifu ikiwa
scopeiliyotolewa ina scopes zenye hatari kubwa au nadra, hasa zile zinazoruhusu upatikanaji wa data kwa wingi au zinaweza kuathiri supply-chain, kama: https://mail.google.com/https://www.googleapis.com/auth/gmail.readonlyhttps://www.googleapis.com/auth/drivehttps://www.googleapis.com/auth/drive.readonlyhttps://www.googleapis.com/auth/chat.messageshttps://www.googleapis.com/auth/chromewebstore
client_id NOT IN approved_client_ids
AND client_id NOT IN last_seen_90d
AND scope CONTAINS any(high_risk_scopes OR rare_scopes)
Majibu / udhibiti:
- Batilisha tokens za OAuth client ID ya hatari:
gam all users delete tokens clientId <client_id>
- Zuia OAuth client ID kwenye Admin Console kwa kuondoa ufikiaji wa programu hiyo kwa data za Google.
Threat hunting pivots:
- Orodhesha apps za nje zilizokubaliwa na watumiaji wachache kuliko N (matumizi nadra).
- Kagua jina la app, publisher, permissions/scopes, na unique application ID.
- Tafuta apps zilizokuwa zikitulia (dormant) ambazo ghafla zinatumia permissions hatari (inawezekana hatua za kufuatia kama internal phishing au wizi wa data).
Mikakati ya Kupunguza Hatari:
- Zuia ufikiaji wa apps za third-party zote (zinazoruhusiwa tu na admin).
- Ruhusu ufikiaji mdogo ili watumiaji waweze kukubali tu taarifa za msingi za profaili za “Sign in with Google”.
Marejeo
- https://www.youtube-nocookie.com/embed/6AsVUS79gLw - Matthew Bryant - Hacking G Suite: The Power of Dark Apps Script Magic
- https://www.youtube.com/watch?v=KTVHLolz6cE - Mike Felch and Beau Bullock - OK Google, How do I Red Team GSuite?
- https://redcanary.com/blog/threat-detection/google-workspace-oauth-attack/
- https://github.com/GAM-team/GAM
Tip
Jifunze na ufanye mazoezi ya AWS Hacking:
HackTricks Training AWS Red Team Expert (ARTE)
Jifunze na ufanye mazoezi ya GCP Hacking:HackTricks Training GCP Red Team Expert (GRTE)
Jifunze na ufanye mazoezi ya Az Hacking:HackTricks Training Azure Red Team Expert (AzRTE)
Saidia HackTricks
- Angalia the subscription plans!
- Jiunge na 💬 Discord group au the telegram group au utufuate kwenye Twitter 🐦 @hacktricks_live.
- Shiriki hacking tricks kwa kutuma PRs kwa HackTricks and HackTricks Cloud github repos.
 HackTricks Cloud
HackTricks Cloud